Cybersecurity continues to evolve as digital systems become more advanced and interconnected. The rise of artificial intelligence has introduced new capabilities in threat detection, monitoring, and response. AI-powered tools can analyze vast amounts of data, identify unusual patterns, and respond to potential threats in real time. These advancements have strengthened the ability of organizations to defend their systems.
Despite these improvements, vulnerabilities still exist, particularly when it comes to databases. Databases store valuable information such as customer data, financial records, and operational insights, making them a prime target for cybercriminals. As data volumes grow and systems become more complex, protecting this information becomes increasingly challenging.
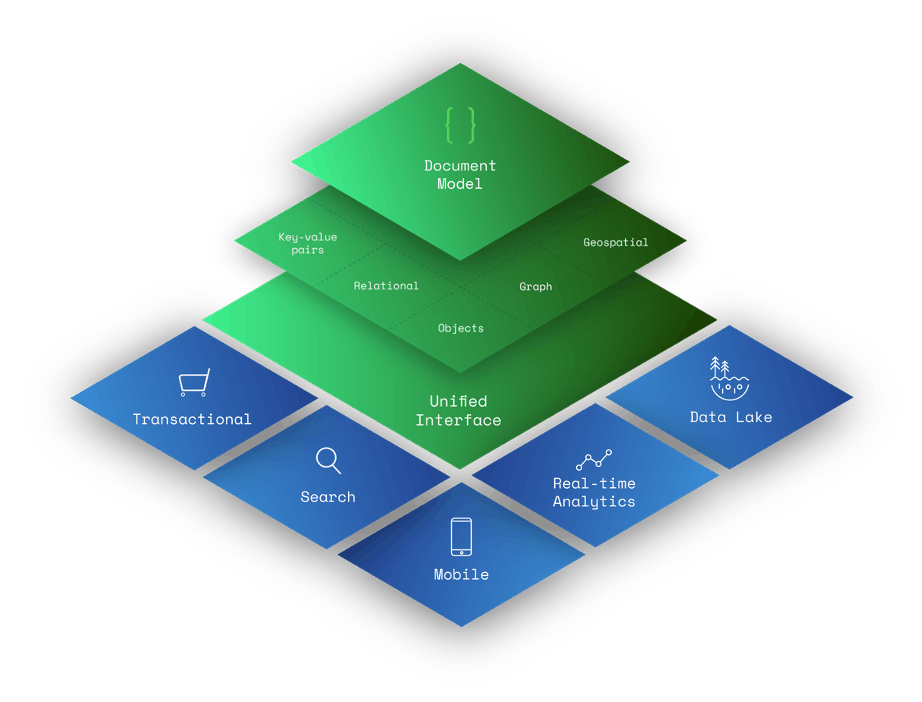
This is where advanced database systems, including document databases, play a critical role. Their architecture and built-in security features provide stronger protection against modern cyber threats.
What Is a Document Database?
A document database is a type of NoSQL database designed to store data in flexible, semi-structured formats, typically using JSON, BSON, or XML documents. Each document contains data in a self-contained structure, allowing for complex and nested information to be stored together. This approach makes document databases highly adaptable, as they can handle varying data types without requiring a fixed schema. Developers can modify and expand data structures without disrupting existing records, making these databases well-suited for modern applications.
Document databases organize data in collections rather than tables, allowing for more intuitive data management. This flexibility supports applications that deal with large volumes of unstructured or rapidly changing data.
How Document Databases Differ from Traditional Databases
Traditional relational databases store data in tables with predefined schemas. Each row must follow a specific structure, which can limit flexibility when handling diverse or evolving data. These systems rely on structured query language for data retrieval and are optimized for transactional operations.
Document databases, by contrast, allow data to be stored in a more natural and flexible format. Each document can have its own structure, enabling developers to work with data in a way that reflects real-world applications.
This flexibility extends to scalability, as document databases are designed to scale horizontally across multiple servers. This makes them suitable for applications that require high availability and performance.
The differences in structure and scalability also influence how document databases approach security, allowing them to implement modern protection mechanisms more effectively.
Encryption and Data Protection
One of the primary ways document databases protect against cybercriminals is through encryption. Data is encrypted both at rest and in transit, ensuring that sensitive information cannot be accessed by unauthorized parties.
Encryption transforms data in document databases into a coded format that can only be read by those with the appropriate keys. This protects information even if it is intercepted during transmission or accessed without authorization. By implementing strong encryption standards, document databases reduce the risk of data breaches and unauthorized access.
Encryption is a foundational security measure that supports compliance with industry regulations and helps maintain user trust.
Access Control and Authentication
Access control is another critical component of database security. Document databases use authentication mechanisms to verify the identity of users and systems before granting access.
Role-based access control allows administrators to define permissions for different users, ensuring that individuals can only access the data they need. This minimizes the risk of unauthorized access and reduces the potential impact of security breaches.
Multi-factor authentication adds an additional layer of security by requiring users to verify their identity through multiple methods. This helps protect against unauthorized access, even if login credentials are compromised.
By implementing strict access control measures, document databases ensure that sensitive data remains protected.
Monitoring and Threat Detection
Continuous monitoring is essential for identifying and responding to cyber threats. Document databases often include tools that track user activity, system performance, and data access patterns.
Advanced monitoring systems can detect unusual behavior, such as unexpected data access or abnormal query activity. These anomalies may indicate potential security threats, allowing administrators to respond quickly. According to research on database security challenges and solutions, monitoring and auditing are key components in preventing and detecting cyber attacks. By maintaining detailed logs and analyzing activity, organizations can identify vulnerabilities and strengthen their defenses.
This proactive approach helps reduce the risk of security incidents and ensures that systems remain secure.
Secure Architecture and Data Isolation
The architecture of document databases also contributes to their security. Many document databases are designed with distributed systems that isolate data across multiple nodes. This reduces the impact of potential breaches, as attackers cannot easily access all data from a single point.
Data isolation techniques, such as segmentation and partitioning, further enhance security by limiting access to specific parts of the database. This approach ensures that even if one section is compromised, the rest of the system remains protected.
Secure architecture also supports high availability, ensuring that systems continue to operate even during security incidents.
Conclusion
As cyber threats continue to evolve, protecting databases has become a critical priority for organizations. Document databases offer a range of security features that help safeguard sensitive information, from encryption and access control to monitoring and secure architecture.
While no system is immune to cyber threats, the advanced capabilities of document databases provide strong defenses against modern attacks. By implementing robust security measures and staying informed about emerging risks, organizations can protect their data and maintain trust with their users.
In an increasingly digital world, the ability to secure data is essential, and document databases play a key role in meeting this challenge.


 The Best Digital Nomad Books to Inspire Your Journey
The Best Digital Nomad Books to Inspire Your Journey